5
1
9781597492072



How to Cheat at Securing Linux available in Paperback, eBook

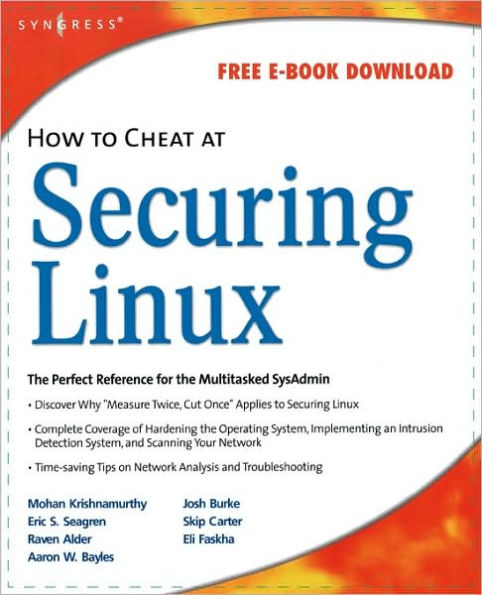
How to Cheat at Securing Linux
- ISBN-10:
- 1597492078
- ISBN-13:
- 9781597492072
- Pub. Date:
- 09/01/2007
- Publisher:
- Elsevier Science
- ISBN-10:
- 1597492078
- ISBN-13:
- 9781597492072
- Pub. Date:
- 09/01/2007
- Publisher:
- Elsevier Science

How to Cheat at Securing Linux
$51.95
Current price is , Original price is $51.95. You
51.95
In Stock

Product Details
| ISBN-13: | 9781597492072 |
|---|---|
| Publisher: | Elsevier Science |
| Publication date: | 09/01/2007 |
| Series: | How to Cheat Series |
| Pages: | 434 |
| Product dimensions: | 0.88(w) x 7.50(h) x 9.25(d) |
About the Author
From the B&N Reads Blog