5
1
9781597490054


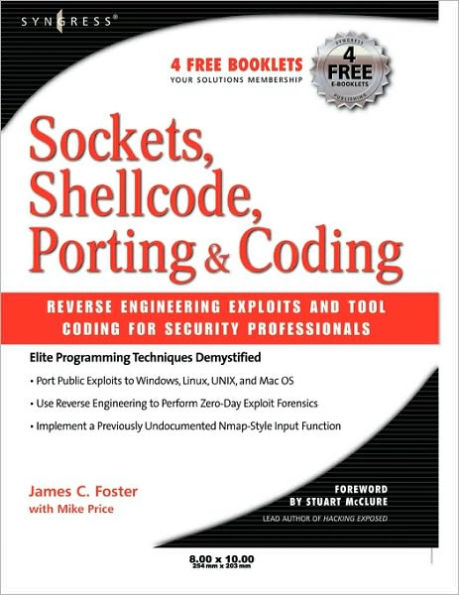
Sockets, Shellcode, Porting, and Coding: Reverse Engineering Exploits and Tool Coding for Security Professionals available in Paperback

Sockets, Shellcode, Porting, and Coding: Reverse Engineering Exploits and Tool Coding for Security Professionals
- ISBN-10:
- 1597490059
- ISBN-13:
- 9781597490054
- Pub. Date:
- 04/12/2005
- Publisher:
- Elsevier Science
- ISBN-10:
- 1597490059
- ISBN-13:
- 9781597490054
- Pub. Date:
- 04/12/2005
- Publisher:
- Elsevier Science
54.95
In Stock

Product Details
| ISBN-13: | 9781597490054 |
|---|---|
| Publisher: | Elsevier Science |
| Publication date: | 04/12/2005 |
| Pages: | 696 |
| Product dimensions: | 6.00(w) x 9.00(h) x (d) |
About the Author
From the B&N Reads Blog